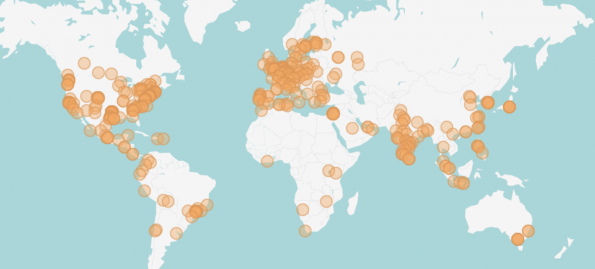
It’s bittersweet to wrap up the third OpenDev in the virtual event series – OpenDev: Containers in Production this week. While it was not the same experience as our traditional in-person OpenDev events, the community made the best of the current situation. This week, we had over 700 people from 470 companies from more than 70 countries who came together to discuss containers in production. Thank you to all the community members who have worked together virtually to collaborate without boundaries.
This event was not possible without the support of the OSF Platinum and Gold members who are committed to the Open Infrastructure community’s success. Also, thank you to the Programming Committee members: Gergely Csatari, Kendall Nelson, Lingxian Kong and Qihui Zhao. You helped to make these discussions possible!
If you didn’t attend—or if you did and want a replay—we have collected the discussions and next steps you may have missed.
Day 1:
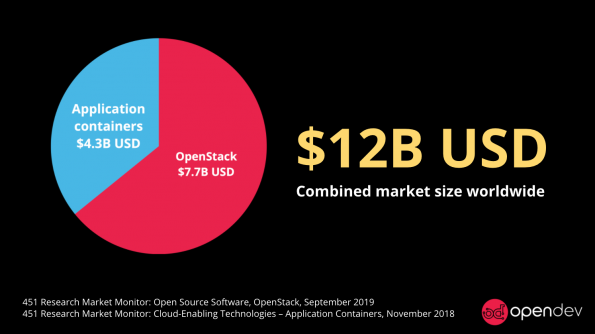
Allison Price, OpenStack Foundation Senior Marketing Manager, and Ashlee Fergerson, OpenStack Foundation Community & Events Coordinator, kicked off the first day of the event by explaining why the OSF chose Containers in Production as one of the OpenDev topics. 451 Research Market Monitor anticipated that the total market revenue of the application containers will reach $4.3 billion by 2022. When it’s combined with the OpenStack market, the total market revenue will reach $12 billion by 2023.
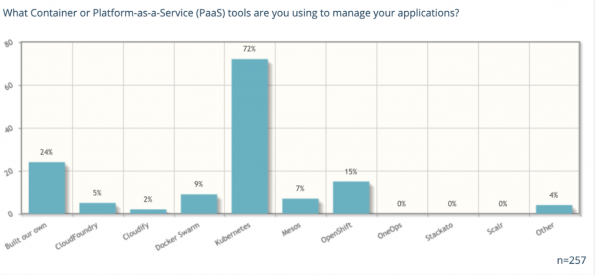
There is not only a huge demand for containers in production, but this also introduces choices for different technology and implementation strategies, so users are facing different integration challenges. According to the data from the most recent OpenStack User Survey about what container or platform-as-a-Service (PaaS) tools users are using to manage their applications, the survey shows that users have different open source components that they are combining into their environments. Just like what Allison said, “it’s not just one size fits all. Every OpenStack user chooses something else to manage their applications based on what makes sense for their own environment.”
Before the discussion began, Xu Wang and Bin Liu from Ant Group gave a demo on monitoring container usage, featuring Kata Containers, Kubernetes, Prometheus and Grafana. They answered questions from the attendees such as if there is a continuous data stream from the shim to the Kata agent to get the metrics and the size of the Virtual Machines (VM) with Kata Containers. If you have missed or would like to rewatch the demo, you can watch the recording here.
Part One: Using OpenStack + Containers Together: OpenStack + Other Container Projects (not k8s)
Part one of OpenDev’s topic on using OpenStack + containers together was moderated by Spyros Trigazis, CERN computer engineer. This discussion was mainly focused on running containers in the environments without Kubernetes. Spyros kicked off the discussion by asking the attendees to share the kinds of images they consume and how they build images. He explained how CERN uses Zuul, which is an open source CI project supported by the OpenStack Foundation, and OpenStack Magnum to build their images. Gergely Csatari, Nokia Senior Specialist, followed up with the questions of what base images CERN uses and how Spyros’ team started them from scratch. The discussion continued with active participants from various companies on topics such as how to use OpenStack and containers together and the requirements users need. Watch the full session recording and catch up with the discussion on the etherpad.
Part Two: Using OpenStack + Containers Together: OpenStack Projects that Interface with k8s (also related projects like Metal3 and Kata Containers)
Part two of the topic on using OpenStack + containers together was moderated by John Garbutt, Stack HPC principal engineer. This discussion was mainly focused on running containers with OpenStack with Kubernetes or with other open source projects. John kicked off the discussion by asking attendees to take polls on where they are with OpenStack and Kubernetes today and what they use to create Kubernetes clusters on OpenStack. The pool results showed that the majority of attendees are already using OpenStack and Kubernetes, and they want to find out more to solve the challenges. In addition, the most popular tools that people use to create Kubernetes clusters on OpenStack are OpenStack Magnum, Rancher, and kubespray. Later, the discussion moved to topics on disposable clusters and long lived clusters and how they change the way people use OpenStack and Kubernetes together. Overall, there were a lot of integration challenges and implementation strategies that the users shared in this discussion session.
If you are interested in discussing further on the performance and accelerators between Kubernetes and OpenStack working together, make sure to join the OpenStack SIGs to continue the discussion. See the discussion notes here and watch the full discussion recording here.
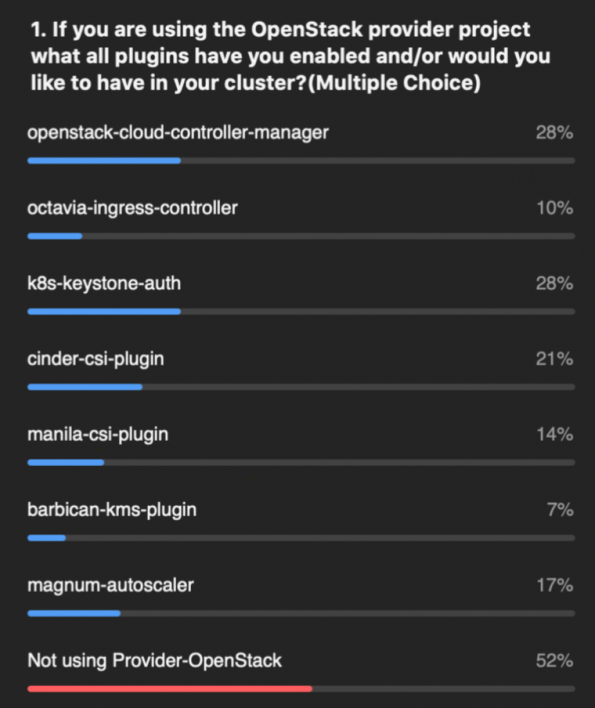
SIG Cloud Provider + Provider OpenStack (openstack w/ k8s)
The moderators, Anusha Ramineni & Christoph Glaubitz, NEC technical specialist & iNNOVO Cloud GmbH cloud architect, kicked off the discussion by giving a brief Introduction on the SIG Cloud Provider and Provider-OpenStack project. This discussion touched on application management on Kubernetes, how Kubernetes deploys on top of OpenStack and how people can use OpenStack to run on top of Kubernetes. Later, the discussion transitioned to how software running in the cluster can help to leverage OpenStack by creating load balancers and more. See the discussion note here and watch the full discussion recording here.

Day 2:
Telco + Network Function
As the moderator for this session, Gergely Csatari, Nokia senior specialist, kicked off the discussion with a question: Why do telecom workloads need additions to Kubernetes to run in production? The discussion touched on topics such as what requirements telecom equipment have, how these requirements lead to the need for different Kubernetes extensions and what kind of network API telcos should have. If you are interested in continuing the discussion on a networking API for Kubernetes, please add your name on line 98 on the etherpad. If you would like to continue the discussion on agreeing on workload separation, please add your name to line 72 here. Watch this discussion recording here.
Security + Isolation
Xu Wang, Ant Group senior staff engineer, led the discussion on security and isolation. This discussion was mainly on container runtimes and management of Kubernetes clusters on top of OpenStack to provide tenant isolation. Users from various companies shared their experiences on the ways to improve the security of containers and protect the host from malicious container apps. Later in the discussion, attendees also shared their best practices and guidance for securing containers. If you are interested in the security Guidance for Telco Network Functions, it is maintained here. If you have missed this discussion or want a replay, check out the discussion recording and read the discussion notes on the etherpad.
Next steps:
Just because the Virtual OpenDev is over doesn’t mean you can’t still experience it! If you would like to watch the previous virtual OpenDev event recordings, you can find them here: Large Scale Usage of Open Infrastructure and Hardware Automation.
Don’t forget to join the open infrastructure community at the next virtual event: Open Infrastructure Summit on October 19-23. The registration is open, and you can register at no cost!
The following week, the Project Teams Gathering will be virtual! The event will be held from Monday, October 26 to Friday, October 30. The event is open to all OSF projects, and teams are currently signing up for their time slots. The schedule will be posted in the upcoming weeks. Register today!

)









